|
|
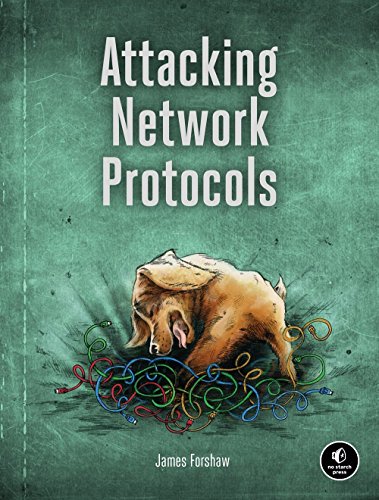
Product Description
Attacking Network Protocols is a deep dive into network protocol security from James Forshaw, one of the world’s leading bug hunters. This comprehensive guide looks at networking from an attacker’s perspective to help you discover, exploit, and ultimately protect vulnerabilities.You’ll start with a rundown of networking basics and protocol traffic capture before moving on to static and dynamic protocol analysis, common protocol structures, cryptography, and protocol security. Then you’ll turn your focus to finding and exploiting vulnerabilities, with an overview of common bug classes, fuzzing, debugging, and exhaustion attacks.
Learn how to:
- Capture, manipulate, and replay packets
- Develop tools to dissect traffic and reverse engineer code to understand the inner workings of a network protocol
- Discover and exploit vulnerabilities such as memory corruptions, authentication bypasses, and denials of service
- Use capture and analysis tools like Wireshark and develop your own custom network proxies to manipulate network traffic
Attacking Network Protocols is a must-have for any penetration tester, bug hunter, or developer looking to understand and discover network vulnerabilities.
Customers Who Bought This Item Also Bought
- Red Team Development and Operations: A practical guide
- Real-World Bug Hunting: A Field Guide to Web Hacking
- Practical Packet Analysis, 3E: Using Wireshark to Solve Real-World Network Problems
- Black Hat Python: Python Programming for Hackers and Pentesters
- Practical Malware Analysis: The Hands-On Guide to Dissecting Malicious Software
- Practical Binary Analysis: Build Your Own Linux Tools for Binary Instrumentation, Analysis, and Disassembly
- Serious Cryptography: A Practical Introduction to Modern Encryption
- Rootkits and Bootkits: Reversing Modern Malware and Next Generation Threats
- Malware Data Science: Attack Detection and Attribution
- Hacking: The Art of Exploitation, 2nd Edition
*If this is not the "Attacking Network Protocols: A Hacker's Guide to Capture, Analysis, and Exploitation" product you were looking for, you can check the other results by clicking this link